This week will be a relatively short blog post about a relatively often seen challenge with the configuration to set the preferred Entra tenant domain name. More specifically, this post will be about the PreferredAadTenantDomainName policy setting. That setting can be used by an IT administrator to basically preconfigure the tenant domain name for the user. Practically that would mean that when the organization uses the @petervanderwoude.nl tenant domain name, this policy setting would be configured with petervanderwoude.nl and would make sure that the user only has to specify their username without the tenant domain name to actually sign in to the device. That can provide a much easier experience.
It does, however, come with some drawbacks that should be taken into consideration. The main drawback is that it will break most of the standard autologon experiences. And, that is applicable to the standard autologon experience during the out-of-box-experience, as well as the kiosk experience. Main reason for that is simply the fact that the tenant domain name will be used with every sign in, and those experiences often rely on local (temporary) accounts. That makes the assignment extra important. This post will provide a brief look at the challenges, the configuration and the eventual user experience.
Looking at the challenges with the preferred Entra tenant domain name
When looking at using the ability to configure the preferred Entra tenant domain name, the configuration on itself is not that exciting. The main things to keep in mind are the scenarios and the assignment of the configuration. And, with that in mind, at least the following experiences are important to differentiate and to handle carefully with this specific configuration.
- For a kiosk experience, with autologon, this configuration should not be used. This configuration would cause the autologon to fail, as the Entra tenant domain name would also be used during that sign in. And, in combination with a local account that would automatically introduce a problem.
- For a regular user experience, with additional sign ins to for example a Remote Desktop Services (RDS) environment, this configuration should not be used. This configuration would cause the Entra tenant domain name to be the default for the RDS sign-in as well. And, when signing in with a different account that would automatically introduce a problem.
- For the regular Windows Autopilot user experience this configuration should be well timed. This configuration could cause the local DefaultUser0 account to break when assigned to devices, as that account is usually being used until the actual user account becomes active. That means that a devices assignment is often not the way to go.
Besides these technical challenges, there is also a functional aspect to keep in mind. The user often already has to use their UPN for accessing many different services. So, for the sake of simplicity it might be easier to do same everywhere.
Note: Keep in mind that this is a list of most common challenges and that it is not a complete list of challenges.
Configuring the preferred Entra tenant domain name
When determined to preconfigure the preferred Entra tenant domain name, it is time to start looking at the configuration itself. The PreferredAadTenantDomainName policy setting is available in the Policy CSP. The setting is available directly via the Settings Catalog with the friendly name of Preferred Aad Tenant Domain Name. And that makes the configuration pretty straightforward. The following eight steps walk through the process of configuring the Entra tenant domain name for the organization.
- Open the Microsoft Intune admin center portal and navigate to Devices > Windows > Configuration profiles
- On the Windows | Configuration profiles blade, click Create > New Policy
- On the Create a profile blade, select Windows 10 and later > Settings catalog and click Create
- On the Basics page, provide at least a unique name to distinguish it from similar profiles and click Next
- On the Configuration settings page, as shown below in Figure 1, perform the following actions and click Next
- Click Add settings, navigate to Account and select Preferred Aad Tenant Domain Name in Settings picker
- Configure the tenant domain name with Preferred Aad Tenant Domain Name to create the expected experience

- On the Scope tags page, configure the required scope tags and click Next
- On the Assignments page, configure the assignment for the required users and click Next
- On the Review + create page, verify the configuration and click Create
Important: Make sure to assign and time the configuration correctly in the environment.
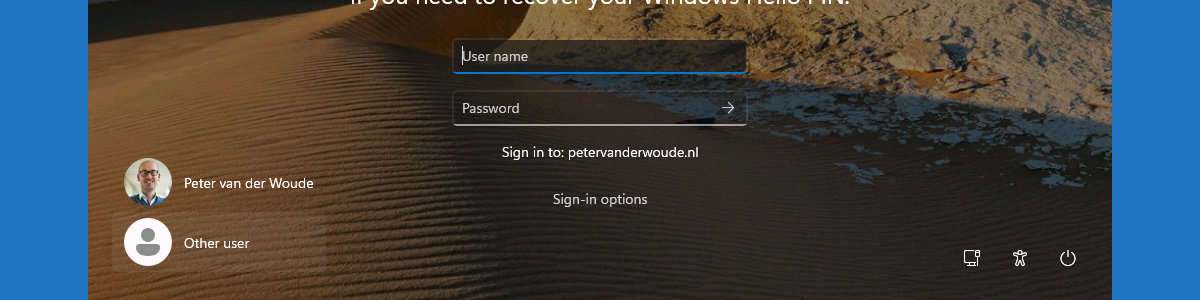
Experiencing the preferred Entra tenant domain name
Especially when sharing the device between multiple users, the configuration can actually be useful. After successfully applying the configuration, it is pretty straightforward to actually experience the configuration. Simply try to logon with another user and the experience should directly be visible, as shown below in Figure 2. That clearly shows the Entra domain name to sign in to. Once that information is shown, every username that will be provided will automatically get the Entra domain name appended during the sign in. A nice and simply experience that has its specific use cases and scenarios.
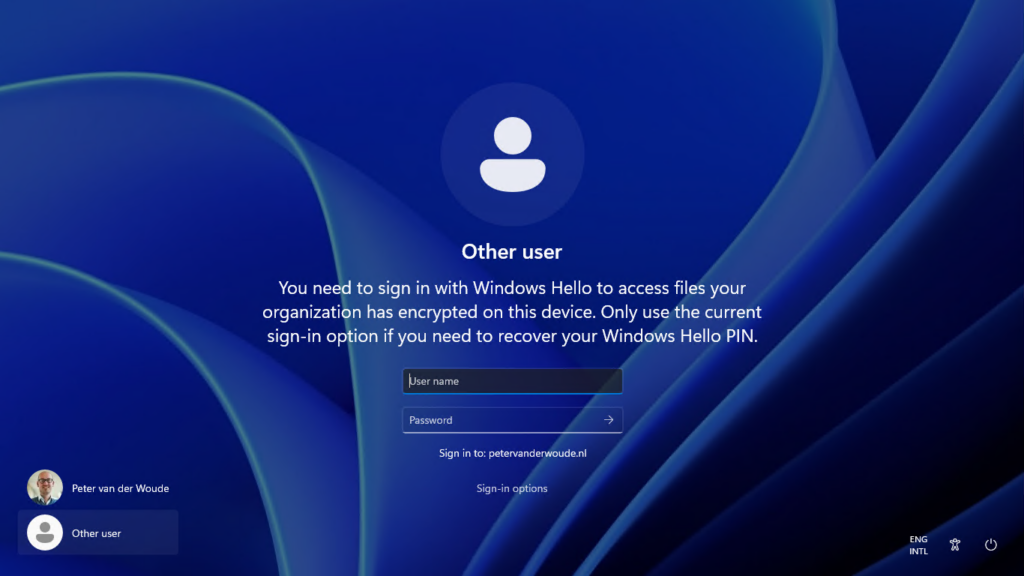
Note: The sign in information shown in Figure 2 is related to the Personal Data Encryption experience.
More information
For more information about configuring the preferred Entra tenant domain name, refer to the following docs.
- Authentication Policy CSP | Microsoft Learn
- Windows Autopilot troubleshooting FAQ | Microsoft Learn
- Assigned Access Recommendations | Microsoft Learn
Discover more from All about Microsoft Intune
Subscribe to get the latest posts sent to your email.

Great write up! Thanks for sharing!!
When you say “Make sure to assign and time the configuration correctly in the environment” can you elaborate on this?
Best to assign yo a user group? What other tinging options are there?
Hi DP,
That could indeed be a workaround. Just keep in mind that it might cause a chicken-egg scenario in the beginning.
Regards, Peter
Well, getting 65000 error on a Win11 enterprise, 25H2 machine.
I am configured to use web login but other resources on the web indicate that it would work with web login.
Hi Michael,
The event viewer might provide you with more details about the failure. This setting can work in specific scenarios, but will also cause issues with other scenarios. Just make sure that it aligns with your scenario.
Regards, Peter